The National Initiative for Cybersecurity Education (NICE) framework is a cybersecurity workforce framework that categorizes and describes the cybersecurity workforce. The 2017 OPM memo directing agencies to assign cybersecurity codes to IT, Cybersecurity, and Cyber-Related functions led to the development of the NICE framework.
<img src=”/assets/images/blog/nice-framework.png” alt=”nice framework” display: block; margin-left: auto; margin-right: auto; width: 50%;”>
The Framework is comprised of the following areas:
- Categories – High-level grouping of standard cybersecurity functions.
- Specialty Areas – Distinct areas of cybersecurity work.
- Work Roles – The most detailed grouping of cybersecurity work comprises specific knowledge, skills, and abilities (KSAs) required to perform tasks in a work role.
These areas, and the Framework as a whole, serve as a central reference to support a workforce capable of meeting an organization’s cybersecurity needs. The National Institute of Standards and Technology (NIST), in their Special Publication on the Cybersecurity Workforce Framework, states that “The NICE Framework provides organizations with a common, consistent lexicon that categorizes and describes the cybersecurity work.” Using the NICE Framework to understand organizational needs and assess how to meet those needs can help an organization plan, implement, and monitor a successful cybersecurity program.
The NICE Framework and TBM
Many agencies have begun implementing the Technology Business Management (TBM) Framework to improve IT management within their organizations. It has been challenging for Agencies to follow a standard approach to allocate Internal Labor costs to the technologies supported in the TBM Framework given the inconsistency of labor and personnel data across agencies. The NICE Framework provides a solution to this challenge.
The NICE Framework can:
- Identify the IT labor workforce inside and outside of the OCIO.
- Provide a solution / business rules for calculating IT specific labor costs from total labor cost.
- Automate allocation of the IT Internal Labor to IT Towers/Resources.
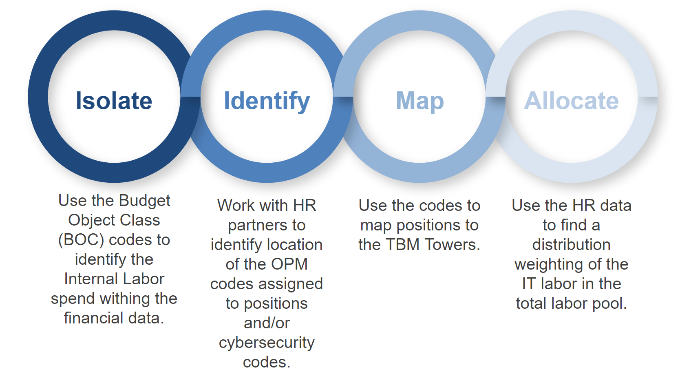
The approach to allocate Internal Labor follows four steps:
- Isolate – Use the Budget Object Class (BOC) codes to identify the Internal Labor spend within the financial data.
- Identify – Work with HR partners to identify location of the OPM codes assigned to positions and/or cybersecurity codes.
- Map – Use the codes to map positions to the TBM Towers.
- Allocate – Use HR data to find a distribution weighting of the IT labor in the total labor pool.
The NICE Framework tool can be explored at https://niccs.cisa.gov/workforce-development/cyber-security-workforce-framework.
For additional information on standard mappings, please refer to the “Mapping Internal Labour Using the NIST_NICE Framework” Max Page here: https://community.max.gov/x/qht-gw or reach out to the FTIM CoP at FTIM-COP@gsa.gov.